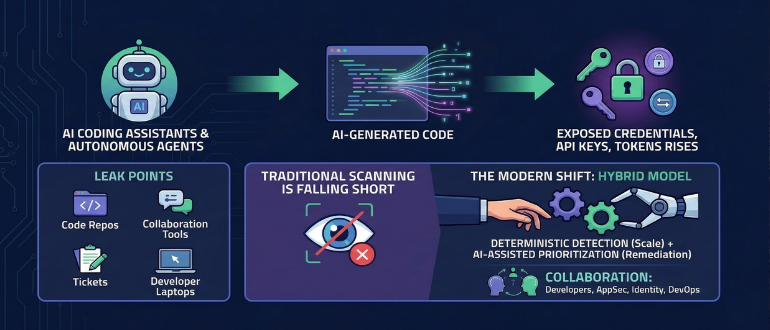
Following a $50 million funding round, GitGuardian CEO Eric Fourrier discusses why secrets security is becoming a much bigger problem in the age of AI-generated code and autonomous agents. As more organizations rush to deploy coding assistants and AI agents, Fourrier argues that the number of exposed credentials, API keys and tokens is rising just as quickly, creating new risks for DevSecOps teams already struggling to manage software supply chain security.
Fourrier explains that AI agents need access to data and systems to be useful, but many organizations are still handling that access the old way by handing over secrets. That, he says, is accelerating an already serious problem. Secrets are ending up in code, collaboration tools, tickets, developer laptops and other places where they can be exposed, reused or stolen. While early concerns focused on whether large language models themselves might reveal secrets from training data, Fourrier says the bigger issue now is how humans are using these tools, especially as non-developers begin building applications with little understanding of secure credential management.
The discussion also highlights how traditional approaches are falling short. According to Fourrier, scanning for secrets at scale still requires deterministic methods because the volume of data across code repositories, binary artifacts, collaboration platforms and cloud environments is simply too large and too costly to hand off entirely to LLMs. Instead, he sees a hybrid model emerging, one that combines fast detection with AI-assisted prioritization and remediation.
Just as important, Fourrier says secrets security can no longer sit with one team alone. Developers, application security teams, identity teams and DevOps leaders all need to work together to prevent leaks, improve remediation and reduce reliance on long-lived credentials. As AI speeds up software creation and expands who can build software, organizations will need new safeguards, better visibility and much tighter collaboration to keep sensitive credentials from becoming the weakest link in the modern development pipeline.