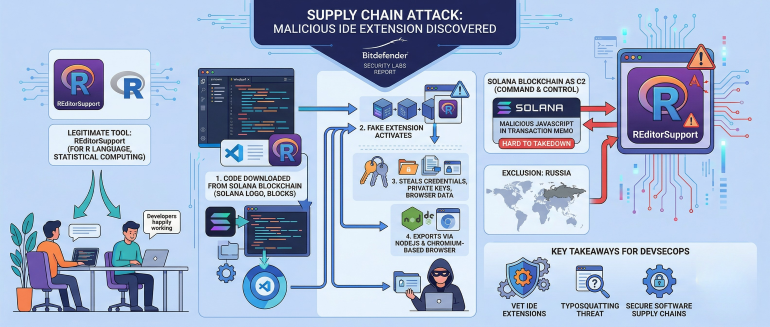
Cybersecurity researchers from Bitdefender, a provider of an endpoint detection and response (EDR) platform, have discovered an extension to the Windsurf integrated development environment (IDE) that steals credentials and data after code is downloaded from the Solana blockchain platform.
Silviu Stahie, a security analyst for Bitdefender, said the extension makes use of typosquatting tactics to make it appear as though it is a legitimate instance of REditorSupport, an extension that provides an IDE to developers that are building applications using the R programming language that is typically used to build statistical computing and data visualization applications.
Windsurf, like most AI coding tools, is based on Visual Studio (VS) Code, an open source AI code editor. The issue that more DevSecOps teams need to be aware of is that fake extensions to tools based on VS Code are now being employed more widely to compromise software supply chains, said Stahie.
In this instance, the extension retrieves encrypted JavaScript code embedded within blockchain transactions and executes it using Node.js runtime primitives that create compiled add-ons to extract data via a Chromium-based browser. Persistence is established using hidden PowerShell code that is used to schedule those tasks.
That approach makes the malware more challenging to detect because instead of relying on traditional command-and-control servers, malicious code stored in a memo attached to a transaction is retrieved from the Solana blockchain to make it nearly impossible to take down the means through which the attack is orchestrated, noted Stahie.
While the exact identity of the cybercriminals that have crafted this attack remains unknown, there is a specific exclusion of systems and developer environments that are located in Russia.
Multiple similar VS Code attacks have previously been discovered. For example, two malicious extensions posing as a harmless “premium dark theme” and an AI-powered coding assistant were discovered late last year. Those extensions were able to capture not only whatever data is on a screen, but also any passwords found in a clipboard.
It’s not clear how much attention is being paid to securing application development tools and platforms. While there has been a lot of focus on ensuring that applications being deployed are more secure, the tools and platforms that application developers use every day are now also a primary attack vector.
Each DevSecOps team should, at this point, conduct a thorough review of the tools and platforms being employed by application developers that all too often don’t pay much attention to where the extensions they add to an IDE come from. Cybercriminals, as of late, have become especially adept at using typosquatting techniques designed to deliberately mislead developers into thinking they have downloaded a legitimate extension to an application development environment only to discover later to their chagrin that the entire software supply chain has been compromised. The challenge, as always, is maintaining the vigilance required to secure software supply chains as developers continue to experiment with all kinds of tooling that in far too many cases has not been properly vetted.